Solutions Shaped For Cloud Security

Data Protection
Cloud security focuses on safeguarding sensitive data stored in the cloud. This includes encryption techniques to protect data both at rest and in transit. Encryption ensures that even if unauthorized individuals gain access to the data, they cannot read or use it without the encryption key.
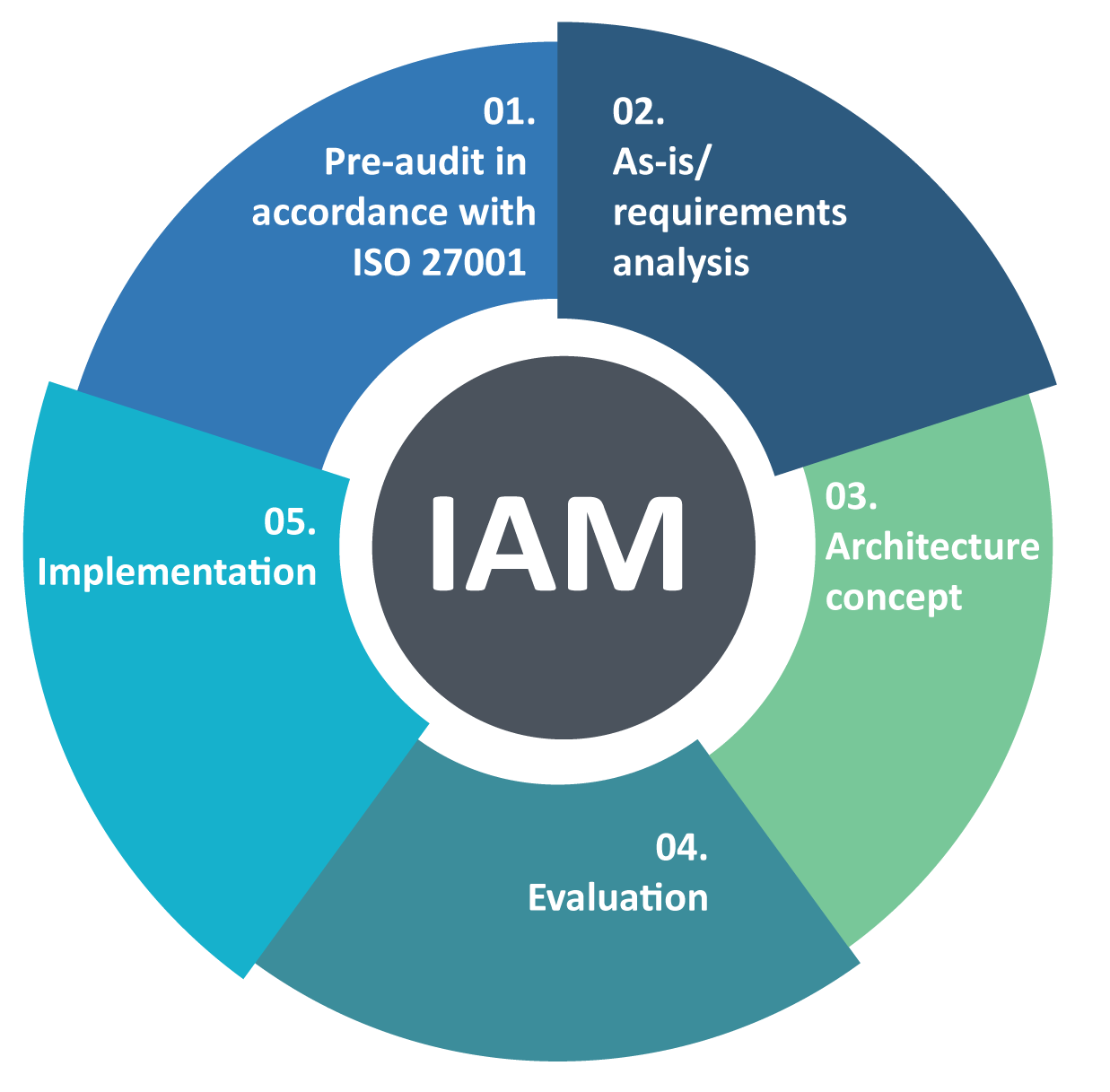
Identity and Access Management (IAM)
IAM plays a crucial role in cloud security by managing user identities and controlling their access to resources. It includes authentication mechanisms, such as multi-factor authentication (MFA), to ensure that only authorized individuals can access cloud services and data.

Secure Infrastructure
Cloud service providers (CSPs) are responsible for maintaining a secure infrastructure. They implement various security measures, including firewalls, intrusion detection and prevention systems, and regular security audits. It is important to work with reputable CSPs that have strong security practices in place.

Vulnerability Management
Continuous monitoring and vulnerability management are essential to identify and address potential weaknesses in cloud systems. Regular vulnerability scans, penetration testing, and patch management help ensure that security vulnerabilities are promptly identified and addressed.
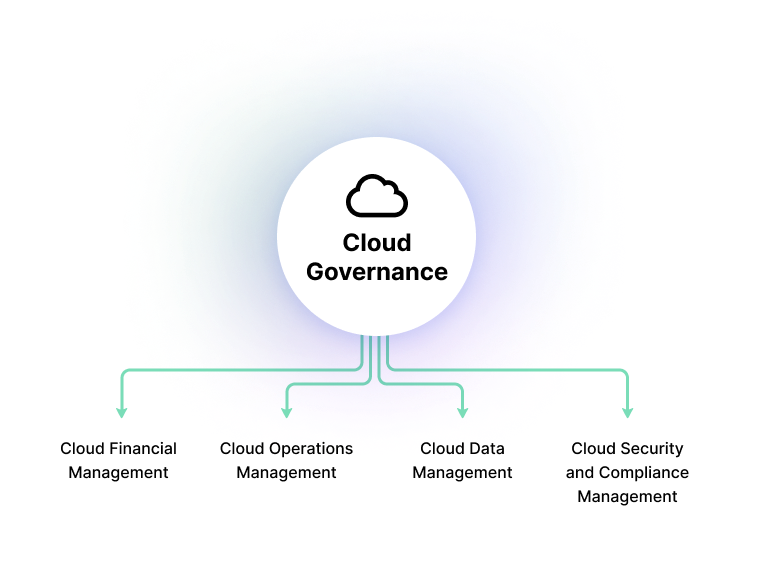
Security Governance and Compliance
Cloud security requires a strong governance framework to define policies, procedures, and guidelines for secure cloud usage. Compliance with industry standards and regulations, such as GDPR or HIPAA, is also crucial. Compliance audits and assessments help ensure that security controls are in place and being followed.

Data Backup and Disaster Recovery
Cloud security includes provisions for data backup and disaster recovery to protect against data loss and service interruptions. Regular backups, redundant storage, and disaster recovery plans help minimize the impact of potential disasters or system failures.

Security Monitoring and Incident Response
Continuous monitoring of cloud environments allows for the detection of security incidents or abnormal activities. Incident response plans and processes should be established to address security breaches, minimize damage, and restore normal operations as quickly as possible.
Employee Education and Awareness
Educating employees about cloud security best practices is vital. This includes training on topics such as strong password management, phishing awareness, and secure data handling. Regular security awareness campaigns help promote a culture of security within the organization.

Data Privacy
Cloud security involves ensuring the privacy of user data. Organizations must comply with privacy regulations and take steps to protect personal information from unauthorized access or disclosure. Privacy-enhancing techniques, such as data anonymization, can be employed to minimize privacy risks.

Threat Intelligence and Response
Staying up-to-date with the latest security threats and trends is critical. Cloud security teams should leverage threat intelligence sources to identify emerging threats and implement appropriate security measures to mitigate risks.
